The importance of cybersecurity for Ukraine, especially in the context of a full-scale war between Ukraine and Russia and the rapid development of artificial intelligence, cannot be overstated. “The Ukrainian Review had a chance to talk in detail about this topic with Serhii Yevchuk, CEO of FS Group, an international company that provides comprehensive cybersecurity services to clients from Ukraine, the United States, Israel, and Europe. He has been working in the field of information security for more than 15 years, specializing in building cybersecurity systems, audits, incident investigations, and implementing innovative solutions.

Yevhen Dzhumyga: Pentagon and White House security consultant Richard Clarke, in his book World Wide War, published in 2010, argues that global cyberwarfare has been going on for a long time. In particular, he gives examples of Russia’s attacks on Estonia and Georgia, and Israel’s attacks on Iran, which obviously means that dictatorial and democratic regimes are confronting each other in cyberspace. Do you share this point of view? Can the global cyber war be considered the “third world war”?
Serhii Yevchuk: Yes, absolutely. We are already living in the reality of cyberwarfare, where conflicts between countries take place not only in the physical but also in the digital space. Sometimes the consequences of such attacks are no less devastating. Disabling critical infrastructure, interference in elections, and information attacks are all tools of modern warfare. This is a struggle between democracies and authoritarian regimes, and it is already underway.
Y.D.: What is Russia’s place in today’s global “hacker” war? Over the past decades, many countries have claimed cyberattacks from the Russians: Estonia, Poland, France, the United States, etc. These included interference in elections, government websites, hacking of databases, and so on. How serious are the challenges posed by Russia to the entire world? Do you think this is a targeted aggressive state policy in the field of cybersecurity? What is the purpose of Russia’s cyberattacks?
S.Y.: Russia is one of the key players in the global hacker war. Over the past two decades, it has been systematically using cyberattacks as a tool of political pressure. We have seen examples of interference in the US elections, large-scale attacks on government websites in Estonia, Poland, and France. These are not chaotic actions – they are part of a state’s aggressive cyber strategy aimed at destabilizing, weakening the enemy and spreading influence.
Y.D.: You represent FS Group, an international cybersecurity company that provides services not only to companies from Ukraine, but also from the US, Israel, etc. Based on your experience, what cybercrimes are currently posing the greatest threat to users and companies around the world and what technologies are most often used by cybercriminals for attacks?
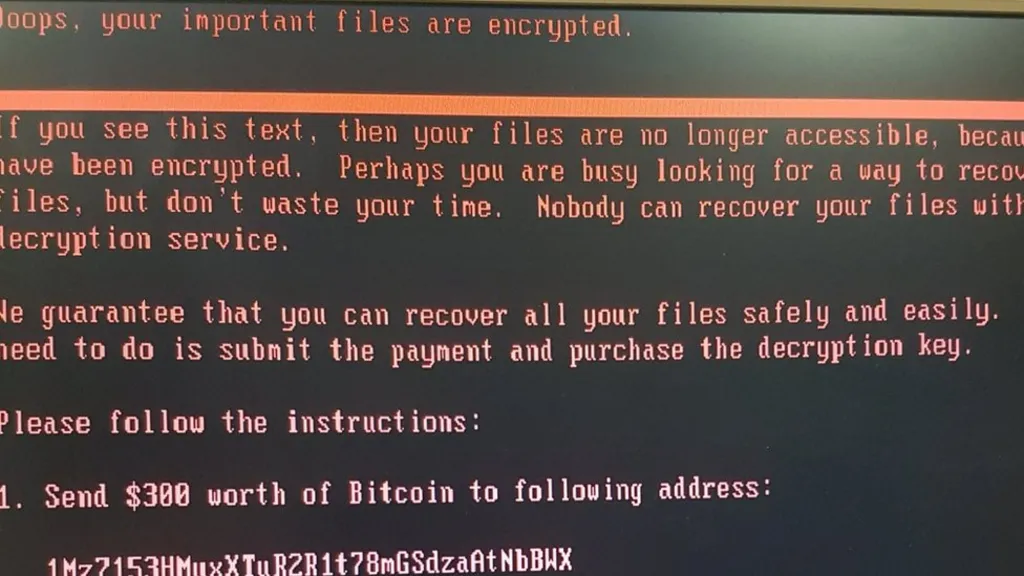
S.Y.: The most common attacks are ransomware, when hackers encrypt data and demand a ransom. Also, many attacks are carried out through phishing and social engineering. APT groups (advanced persistent threats) are extremely cautious: they first conduct reconnaissance and then launch a targeted attack. Attackers also use AI to automate attacks, generate malicious code, or deepfake videos.
Artificial intelligence\Photo: Unsplash
Y.D.: How exactly is artificial intelligence used in the development of cybercrime and what are the possibilities of using AI to counteract cybercrime?
S.Y.: AI has become a powerful tool in the hands of both defenders and attackers. Hackers use it to create more believable phishing emails and automate the detection of vulnerabilities in systems. But AI also allows us to improve the effectiveness of cyber defense: detect anomalies in traffic, predict attacks, and respond quickly to incidents. This is a race of technologies, and we have to be one step ahead.
Y.D.: How big of a threat is the human factor in cybersecurity (for example, the attack on Kyivstar was carried out through the account of one of its employees)? Or are cyberattacks primarily about technology?

S.Y.: Most often, vulnerabilities lie not in the technology itself, but in people. The attack on Kyivstar is a good example: the attackers gained access to the system through an employee’s account. But this is just one of the scenarios.
There are two main ways in which attackers gain access:
Through bribery or social engineering – when an employee grants access knowingly or accidentally.
Through credential compromise – when access to accounts is gained through malware (e.g., infostealers) or the use of so-called combo lists (large merged databases of logins and passwords from previous hacks).
Therefore, organizations need not only to train employees but also to constantly monitor accounts, detect their appearance in the darknet, and implement early warning systems for leaks. After all, compromised accounts often become the entry point for large-scale attacks such as ransomware, data encryption, sabotage, or espionage.
Cybersecurity is not only about technology, but also about culture, training, and real-time monitoring.

Cybersecurity. Photo: unsplash
Y.D.: Ukraine is currently ranked 16th in the NCSI cybersecurity index, ahead of the UK and Ireland, for example. Can we say that we are well protected from cyberattacks and can become a leading partner in cybersecurity for Europe? If so, how can the Ukrainian experience of countering cyberattacks be useful for European countries?
S.Y.: Undoubtedly, we have a unique experience. Ukraine resists cyberattacks in real war conditions – not in laboratories, but on the battlefield. Our specialists are highly trained, and we are already partners for many Western companies and governments. Ukraine’s experience is practical cyber defense in the face of maximum threat. A logical step for Ukraine would be to establish cooperation not only with Europe but also with NATO in the field of cybersecurity through joint training and experience exchange. These initiatives will be extremely useful for both Ukraine and European countries in general.
Y.D.: Of course, the full-scale invasion has had a significant impact on cybersecurity and cybersecurity risks for our country. Ukrainians felt the consequences of cyberattacks on Kyivstar in December 2023 and attacks on the websites of the National Information Systems (NIS) and the Ministry of Justice of Ukraine. How can the Ukrainian state successfully counter these challenges, especially given the full-scale invasion?
S.Y.: It is necessary to develop public-private partnerships, invest in the cyber reserve, support the expert community, and develop early threat detection tools. Close cooperation with international partners is also critical: intelligence sharing, joint training, integration into the Western security infrastructure.
Y.D.: To what extent is Ukraine’s cybersecurity legislation adapted to the requirements and norms of the European Union? In connection with the signing of the Association Agreement with the EU in 2014 and the granting of the candidate status for accession to the European Union, is there any work being done to unify national and European legislation? What laws do we need to change and develop to achieve European standards?
S.Y.: We are moving in the right direction. We are already implementing regulations adapted to European directives, in particular NIS2. But we still need to update a number of regulations, in particular on incident management, certification of specialists, and liability for violations. This is necessary for integration into the European digital space.
Y.D.: In recent years, we have seen numerous cases of account hacking, spreading links with viruses, etc. on social media. How would you assess the level of cybersecurity education in Ukraine? How can the level of education of Internet users be improved and how much will it help to avoid cyberattacks on personal devices?
Account hacking. Photo: unsplash
S.Y.: Unfortunately, it is still insufficient. The private and public sectors suffer from a low level of so-called cyber hygiene. People often neglect basic rules: weak passwords, opening suspicious emails, installing unverified programs. To improve security, massive educational initiatives are needed: starting with schools, universities, and civil servants. Many people know the People-Technology-Processes triad. People are the first line of defense, and they need to be trained.
Yevhen Dzhumyga